Daily Bug challenge Shady Oaks Finance

Hey everyone 404yeti here and today we will go over a quick web app challenge from bug forge
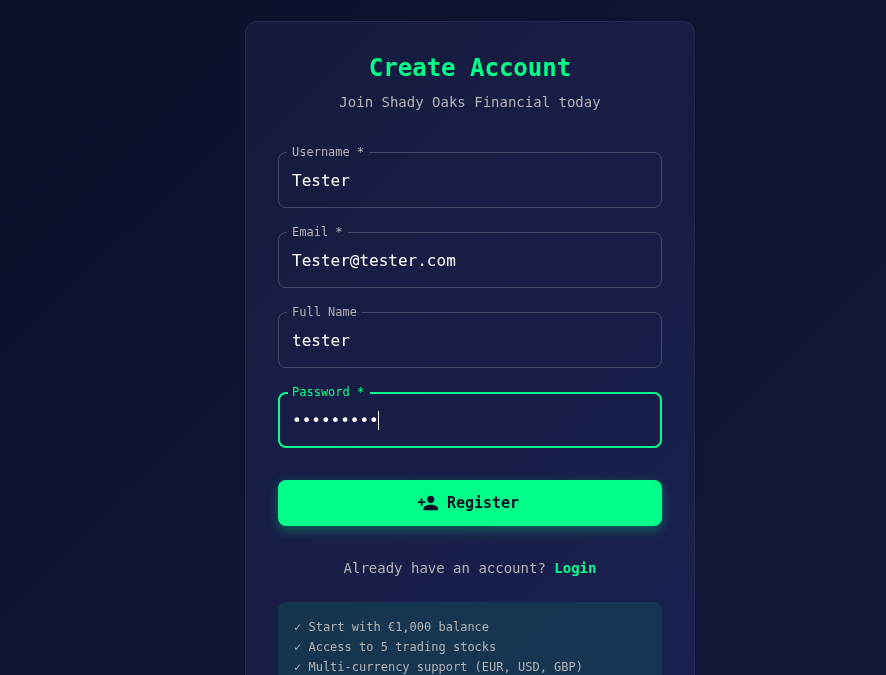
Step 1 make a user account
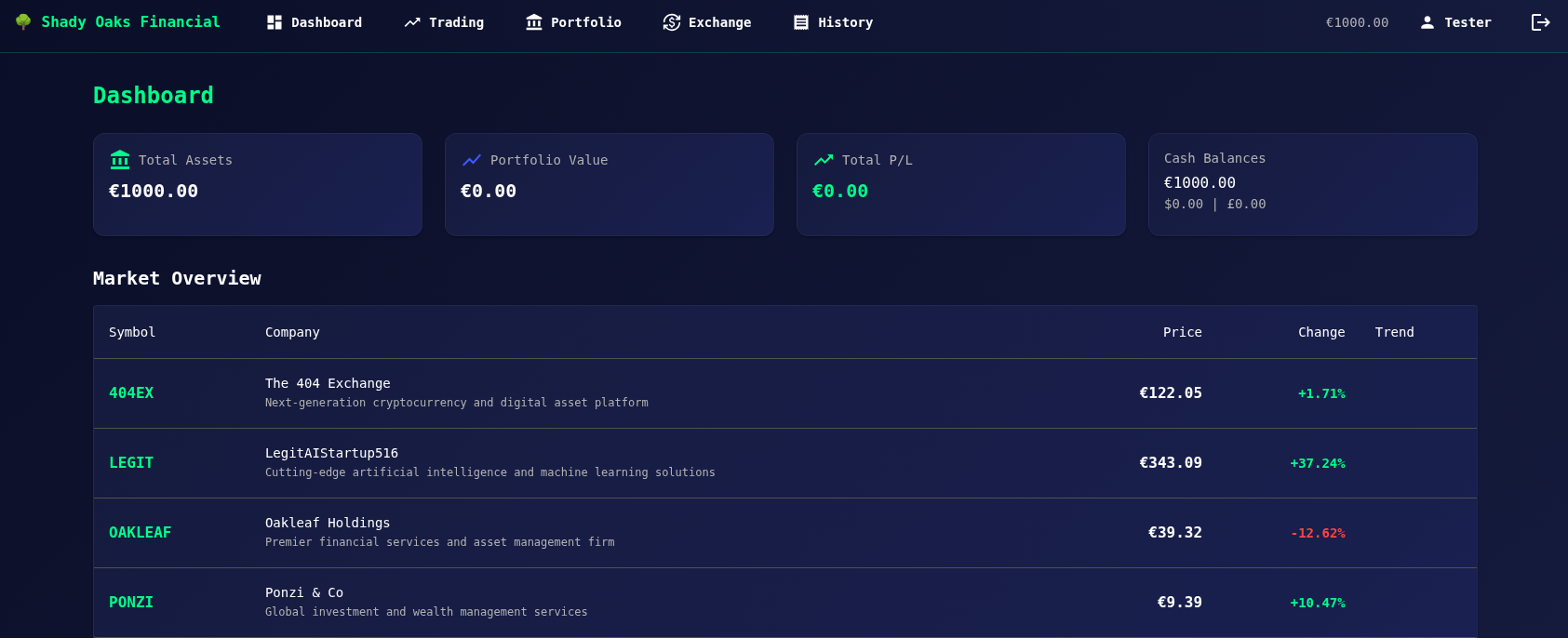
Here we can see our financial dashboard
Step 2 change the api endpoint to /admin
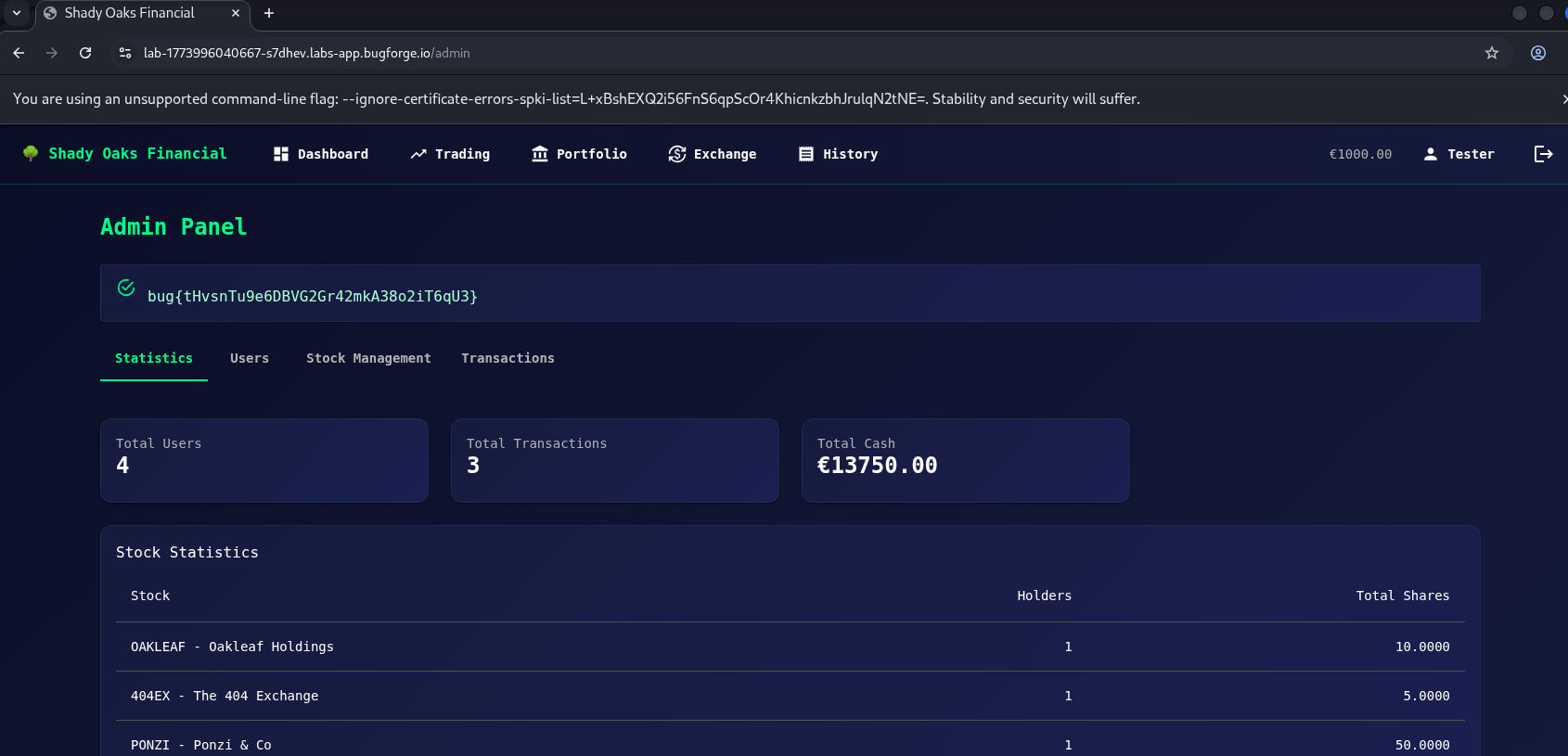
While looking at the requests, I noticed the application was calling an API endpoint.
Instead of jumping straight into fuzzing or injections, I tried something simpler.
In Caido / the browser request, I changed the endpoint to:
/admin
BOOM
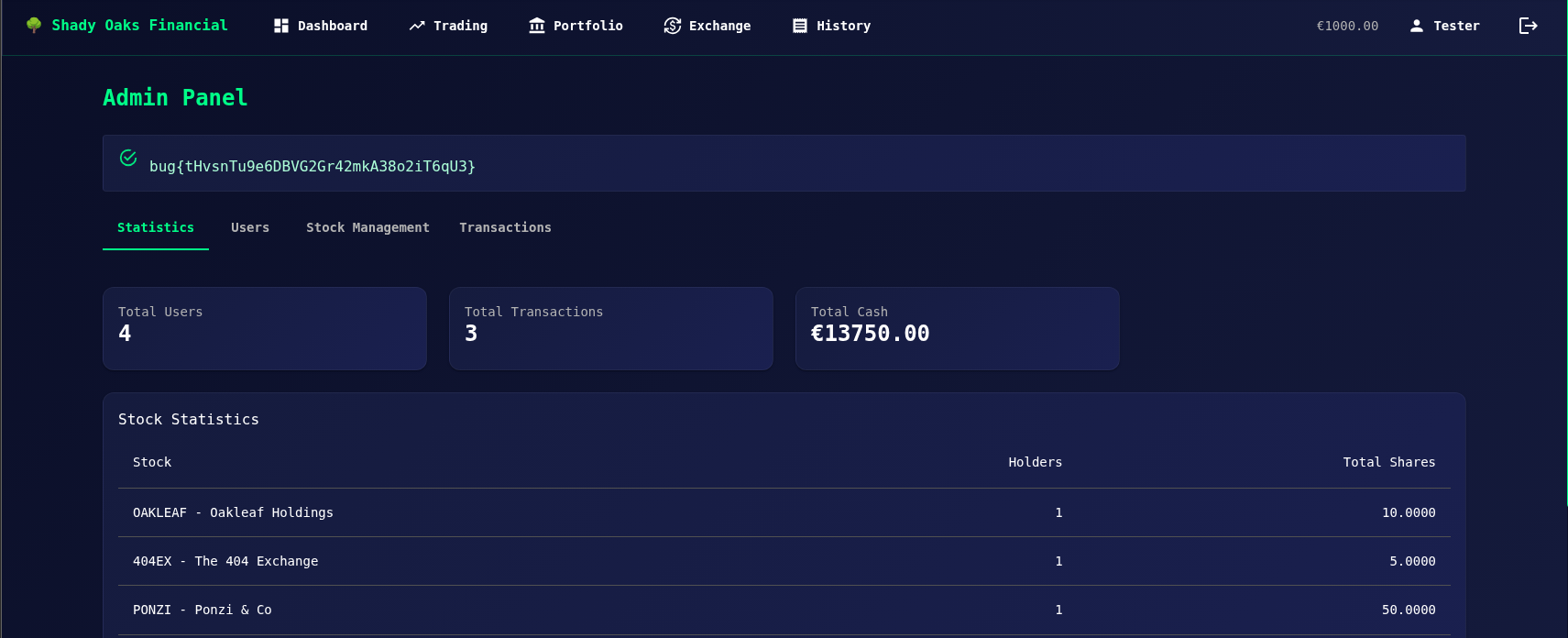
we got admin panel access!
Why this important
A lot of people go straight for:
- SQL injection
- XSS
- fuzzing
- brute force
But many real vulnerabilities come from simple mistakes like:
- exposed admin routes
- missing authorization checks
- forgotten endpoints
- insecure API paths
Testing common endpoints manually can save a lot of time.
Sometimes the easiest attack is just:
Try the obvious thing first.
Final Thoughts
This was a quick challenge, but a good reminder that good pentesting starts with exploration, not exploitation.
Look at the requests.
Change parameters.
Try common endpoints.
Stay curious.
More Bug Forge writeups coming soon.
Stay frosty. ❄️
— 404Yeti